The modern global trade network currently faces an unprecedented wave of sophisticated criminal activity that threatens to dismantle the fragile stability of international commerce. Professional syndicates no longer rely on simple smash-and-grab tactics to acquire valuable goods; instead, they operate as highly organized, tech-savvy enterprises with global reach. These networks identify vulnerabilities within maritime passages and terrestrial corridors, turning logistics into a high-stakes battleground for security experts and mutual insurers.
Consulting agencies now track a shift where traditional theft is replaced by surgical strikes against the most exposed links in the chain. This evolution reflects a broader trend toward organized crime infiltrating digital infrastructure to predict cargo movements. As a result, the industry must move beyond basic physical barriers and look toward integrated security frameworks that address both physical and digital threats simultaneously.
Evolving Criminal Tactics and Statistical Growth Patterns
From Brute Force to Cyber Fraud: Emerging Patterns in Theft
Criminals increasingly utilize fictitious pickups by leveraging stolen identities and fraudulent documentation to walk away with entire shipments without firing a single shot. By exploiting logistics cybersecurity, these groups facilitate complex brokering scams that mislead drivers and warehouse managers. This digital deception allows illicit actors to redirect shipments of rare earth minerals and specialized commodities that are far more difficult to trace than standard consumer goods.
There is also a noticeable shift in high-value targets as criminal interest migrates from common electronics toward high-stakes specialized cargo. Recent incidents, such as a multi-million dollar smartphone heist at a major international airport, demonstrate the audacity of these operations. As these patterns become more prevalent, the industry faces the daunting task of securing virtual paperwork as rigorously as the physical containers themselves.
Quantifying the Surge: Data-Driven Performance Indicators and Projections
Statistical data reveals a grim picture of the current landscape, with global sea piracy rising by 85 percent recently. The Strait of Malacca has become a particular flashpoint, witnessing a critical 281 percent spike in reported incidents. These numbers suggest that maritime security protocols have not kept pace with the tactical flexibility of regional pirate networks.
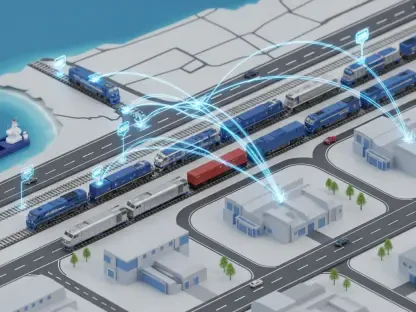
On land, the situation remains equally precarious as rail theft in the United States has jumped from 4 percent to 10 percent of total reported incidents. This growth in terrestrial risk directly impacts global insurance premiums, forcing companies to reconsider the financial viability of certain transit routes. The economic burden of these high-profile heists extends far beyond the immediate loss of goods, affecting every level of the global economy.
Navigating the Most Critical Obstacles to Supply Chain Integrity
The Human Element: Addressing Insider Threats and Employee Complicity
One of the most unsettling trends in cargo security is the role of internal assistance, with over one-fifth of all thefts involving some form of employee complicity. Whether through coercion or financial incentive, insiders provide the precise timing and location data required for successful heists. Addressing this vulnerability requires a fundamental shift in personnel vetting and internal security protocols to ensure that trust is verified at every level of the organization.
Moreover, the complexity of modern logistics makes it difficult to maintain oversight over every individual with access to sensitive shipping data. Improving internal security is not just about background checks but also about creating a corporate culture where security is a shared responsibility. Without addressing the human element, even the most advanced technological defenses remain susceptible to subversion from within.
Infrastructure and Technology Gaps: Overcoming Logistics Blind Spots
A significant challenge remains the disparity between rapid criminal adaptation and the slow pace of corporate security upgrades. Many logistics firms still rely on unmonitored load boards and loosely regulated subcontracting, which provide perfect entry points for fraudulent actors. These blind spots in the supply chain allow criminals to insert themselves into legitimate transactions with minimal effort.
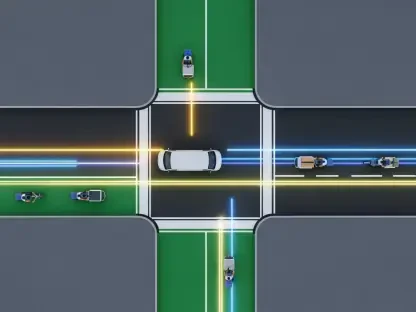
To mitigate these risks, companies must invest in infrastructure that provides real-time visibility across the entire transit journey. Relying on legacy systems in a world of digital-first crime is a recipe for continued loss. Closing these technological gaps requires a commitment to transparency and a willingness to overhaul outdated subcontracting models that prioritize speed over security.
Strengthening Governance and Regulatory Compliance Frameworks
Tighter oversight for digital load boards and transport marketplaces is no longer optional but a necessary requirement for market participation. Regulators are beginning to implement rigorous vetting standards for third-party carriers to prevent fraudulent entities from accessing sensitive cargo. This shift toward mandatory verification helps ensure that only legitimate, vetted providers can operate within the logistics ecosystem.
Furthermore, compliance requirements for tamper-evident sealing and advanced GPS tracking are becoming standardized across various jurisdictions. Government-led scanning mandates for international shipping play a vital role in deterring theft by increasing the likelihood of detection. These regulatory frameworks provide a baseline of security that forces all stakeholders to adhere to a minimum standard of cargo protection.
Proactive Defense: The Future of Intelligence-Led Logistics
The industry is currently transitioning from reactive security measures toward dynamic, commodity-specific risk assessments that anticipate threats before they manifest. Advanced scanning technology and real-time visibility tools allow logistics firms to monitor cargo health and location with pinpoint accuracy. This proactive stance enables companies to alter routes or increase security presence based on live intelligence.
Future market disruptors like artificial intelligence and blockchain are poised to revolutionize cargo authentication by providing immutable records of every transaction. Cross-agency intelligence sharing between private firms and law enforcement further bridges the gap in information, making it harder for criminal networks to hide. By embracing these technologies, the logistics sector can build a more resilient and transparent network.
Strategic Imperatives for Securing the Future Global Supply Chain
The deepening crisis of global cargo theft necessitated a fundamental reimagining of how goods are protected in transit. Stakeholders across the world recognized that the traditional methods of securing cargo were insufficient against the sophisticated methods of modern criminal enterprises. This awareness drove a massive push for collaboration between technology providers, law enforcement, and logistics operators to create a more unified front against illicit activity.
Investment in transparency-driven oversight and resilient infrastructure became the cornerstone of the industry’s response. Leaders prioritized intelligence-led mitigation as a core business necessity, moving away from the idea that security was merely a cost center. These strategic imperatives successfully shifted the balance of power, as the integration of advanced tracking and rigorous vetting standards established a new baseline for global supply chain integrity.